While computing resources are computational systems responsible for data analysis and storage, misusing these devices can lead to risks of privacy exposure and malicious exploitation (ScienceDirect). Common threat models include misconfigured data storage, which occurs on cloud platforms like AWS and Azure, exposing sensitive data due to improper storage bucket settings. For example, in the 2019 Capital One case,an attacker stole the credit information of over 100 million US and Canadian users through a misconfigured AWS S3 bucket (ACM).
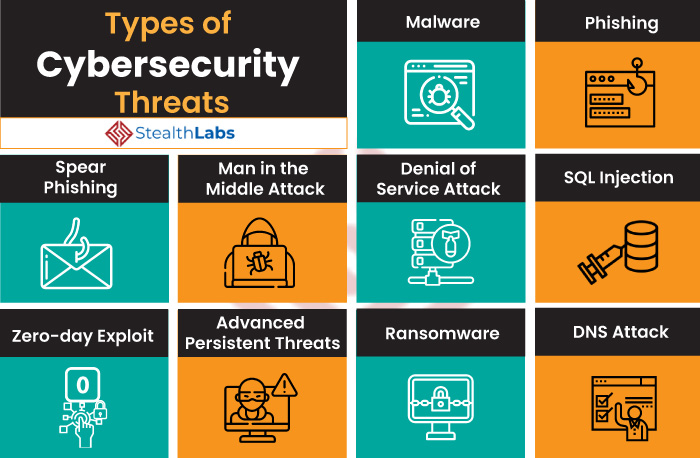
Resource hijacking, on the other hand, compromises privacy through methods such as Virtual Machines, phishing, or cryptocurrency mining malware. API abuse makes unprotected REST APIs susceptible to DDoS attacks, potentially causing server crashes. Additionally, granting employees or third parties excessive access can lead to insider privilege abuse, where critical data and resources are deleted or even misused in illegal online activities.
The misuse of computing resources not only results in direct economic loss, but, more importantly, damages al platform’s’ brand credibility and reputation. To effectively counteract these threats, according to Rackware, enterprises can implement security measures, including strict access controls, continuous monitoring, and well-defined incident response plans. Misconfigurations can be identified through technologies enforcing strict identity and access control, utilizing IAM (Identity and Access Management) to prevent unauthorized access and account takeovers. Last but not least, ensure API security through authentication, access control, and continuous monitoring to prevent unauthorized access and exposure of API keys. Access to sensitive data should be restricted to authorized personnel based on the principle of least privilege (PoLP). These are common ways to prevent and address the misuse of computing resources.